To create an standard access list on a Cisco router, the following command is used from the router’s global configuration mode:
R1(config)# access-list ACL_NUMBER permit|deny IP_ADDRESS WILDCARD_MASK
NOTE
ACL number for the standard ACLs has to be between 1–99 and 1300–1999.
extended ACLs has to be between 100–199 and 2000–2699.
You can also use the host keyword to specify the host you want to permit or deny:
R1(config)# access-list ACL_NUMBER permit|deny host IP_ADDRESS
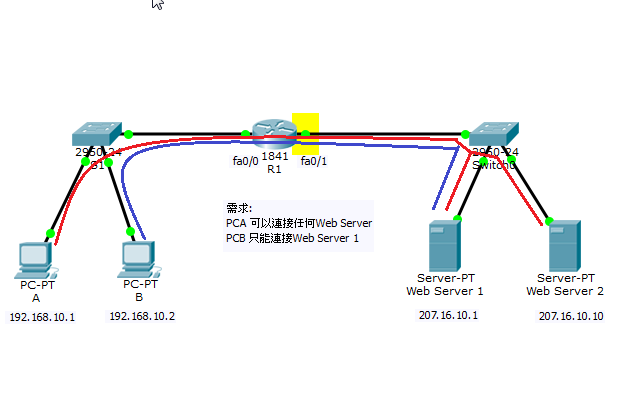
Once the access list is created, it needs to be applied to an interface. You do that by using the ip access-group ACL_NUMBER in|out interface subcommand. in and out keywords specify in which direction you are activating the ACL. in means that ACL is applied to the traffic coming into the interface, while the outkeyword means that the ACL is applied to the traffic leaving the interface.
* IPv6 不支援 standard ACLs
R1(config)#access-list ?
<1-99> IP standard access list
<100-199> IP extended access list
R1(config)#access-list 10 permit ?
A.B.C.D Address to match
any Any source host
host A single host address
R1(config)#
access-list 10 permit 192.168.10.1
R1#sh access-lists
Standard IP access list 10
10 permit host 192.168.10.1